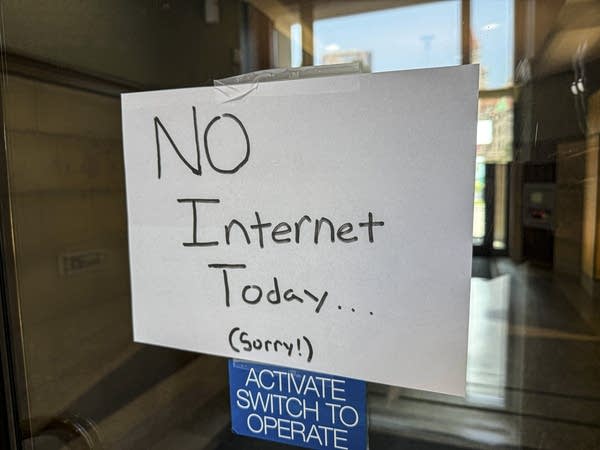
Winona County is in the midst of responding to a cyberattack on its IT network which has seriously impacted its systems. Gov. Tim Walz’s office said the country requested and is now receiving help from the Minnesota National Guard “due to the scale and complexity of the incident.” It’s the second cyberattack on the county already this year.
On Wednesday, Winona County Administrator Maureen Holte said in a statement that the county has taken its systems offline, “out of an abundance of caution,” while it works to secure and restore services safely. Holte said the public should expect system delays as a result, but added that there has been no interruption to emergency services. The county has not provided further updates on the attack’s impact as of Thursday morning.
“Cyberattacks are an evolving threat that can strike anywhere, at any time,” Minnesota Gov. Tim Walz said in the statement Wednesday. “Swift coordination between state and local experts matters in these moments. That's why I am authorizing the National Guard to support Winona County as they work to protect critical systems and maintain essential services.”

The county declared a local state of emergency as it works to resolve the issue. Besides the National Guard, Winona County also notified the FBI and Minnesota cyber resources, and is working with third-party cybersecurity and data forensics consultants in its investigation.
Winona County was the target of another cyberattack earlier this year in January, as these sorts of crimes against local units of government become more common. County officials say the attacks appear to have been perpetrated by different criminal actors, according to a preliminary investigation. Rochester Public Schools was targeted by a cyberattack in 2023, and just last summer, the city of St. Paul experienced a massive ransomware incident that also required assistance from National Guard deployment and forced the city to shutter parts of its network.
According to the state’s 2025 Cybersecurity Incident Report, attacks against federal, state, and local governments are rising in frequency and sophistication. The report indicates that 269 public entities and government contractors in Minnesota reported possible cybersecurity incidents last year.
“Cyber attackers have gotten really good at hacking humans,” said John Israel, the state of Minnesota’s chief information security officer. “They're finding ways to really trick people. They've turned this into a business operation with very mature teams that are focused on finding vulnerabilities, exploiting them and getting to the maximum impact that they can.”
Israel said that, in the past, criminal agents were more focused on breaking into an organization's system, locking it down, and charging ransoms to unlock the files. But as more organizations have gotten better at backing up their systems, cyber attackers have evolved. Now, they are not only encrypting and locking down systems, they’re also extracting and stealing data first that they can hold hostage — threatening to release it if the organization doesn’t pay the ransom.
“We call it kind of a double extortion event,” Israel said.
Government entities aren’t the only ones experiencing these incidents, but Israel said state and local governments have become lucrative targets. And they tend to be more vulnerable because government entities’ systems often are connected to outside partners and contractors, and they’re focused on being open and accessible to the public to provide essential services, leaving more cracks and openings for cybercriminals to exploit.
“This just comes with the nature of government,” Israel said. “Threat actors are really good about finding those holes and finding those ways in. [Governments have] got to be right 100% of the time, whereas bad actors really have to just be right one time to get in and cause impact.”
Israel explained that the cybercriminals who launch these attacks are primarily financially motivated and rarely local. The perpetrators are often part of overseas groups that have made a business out of extorting entities like Winona County.
There are things local governments — and any organization — can do to better protect themselves and more easily recover their system without paying the ransom.
First is investing in a good offline back up system, so that data can be recovered in the case of a ransomware incident. Second is investing in core security systems, like an endpoint detection and response platform, which proactively helps identify and respond to cyberthreats on devices and the use of multifactor authentication on every account.
Israel said these preventative measures can allow organizations to restore everything from the back up system, basically wiping the system clear and starting fresh.
“That’s the strongest thing that we’ve seen organizations invest in over the years,” Israel said.